Table of Contents
- What Is First-Party Fraud
- First-Party Fraud vs Third-Party Fraud
- Common Types of First-Party Fraud
- First-Party Fraud in Banking and Financial Services
- How First-Party Fraud Impacts Organizations
- First-Party Fraud Detection Methods
- Challenges in Detecting First-Party Fraud
- First-Party Fraud in Hiring and Recruiting
- Detecting Fraud in Recruiting With Tofu
- Final Thoughts
- FAQs
What is first-party fraud? It's when the person applying for credit, filing the claim, or submitting the job application is using their real identity with zero intention of following through. No stolen credentials, no impersonation, no fake documents. Just a real person whose plan from the start was to default, dispute, or disappear. That's why it now represents 36% of all fraud cases globally, up from 15% a year ago. Your identity verification passes them through cleanly because there's nothing false about who they are. The lie is about what they're going to do next, and that doesn't show up in a database lookup.
TLDR:
- First-party fraud happens when someone uses their real identity to deceive—no stolen credentials needed.
- It accounts for 36% of all fraud worldwide, up from 15% the prior year, doubling its share in 12 months.
- Traditional fraud detection fails here because identity checks pass—the fraud is in intent, not identity.
- In hiring, 45% of false document submissions now occur in employment sectors, creating insider threats.
- Tofu detects first-party fraud in recruiting using 40+ signals, network intelligence, and deepfake detection.
What Is First-Party Fraud
First-party fraud is when a real person uses their own identity to commit fraud. No stolen credentials, no impersonation, no third-party schemes. The fraudster is the customer, the applicant, the account holder. They're using their actual name, their real Social Security number, and their genuine contact information to deceive.
That's exactly what makes it so difficult to catch.
Traditional fraud detection looks for signs that someone isn't who they claim to be. With first-party fraud, the identity checks pass because the person applying is genuinely that person. They just have no intention of repaying that loan, honoring that transaction, or delivering on whatever obligation they just signed up for.
The scope of the problem is growing fast. First-party fraud now accounts for 36% of all reported fraud incidents worldwide, up from just 15% the year prior. That's not a gradual drift. That's a category doubling its share of the fraud mix in a single year.
Where third-party fraud relies on deception about identity, first-party fraud relies on deception about intent. The person is real. The lie is about what they plan to do next.
First-Party Fraud vs Third-Party Fraud
The distinction sounds simple. In third-party fraud, someone steals your identity and uses it without your knowledge. In first-party fraud, you are the fraudster. But that single difference has massive downstream consequences for how you detect and stop each one.
Third-party fraud leaves a trail of anomalies. The name doesn't match the device. The location is unfamiliar. The behavioral patterns are off. Detection systems are built to catch exactly this kind of mismatch, and they're reasonably good at it.
First-party fraud leaves almost no trail at all.
When a real person applies for credit with their real name and real documents, every identity signal checks out. The fraud isn't in the identity. It's in the intention. And intentions don't show up in a database lookup.
Second-party fraud sits in between. A second-party fraudster knowingly shares or lends their identity to someone else committing fraud. Think of a family member opening an account on behalf of a fraud ring, fully aware of what's happening. The identity is real, the consent is real, but the purpose is criminal.
Here's how the three categories compare:
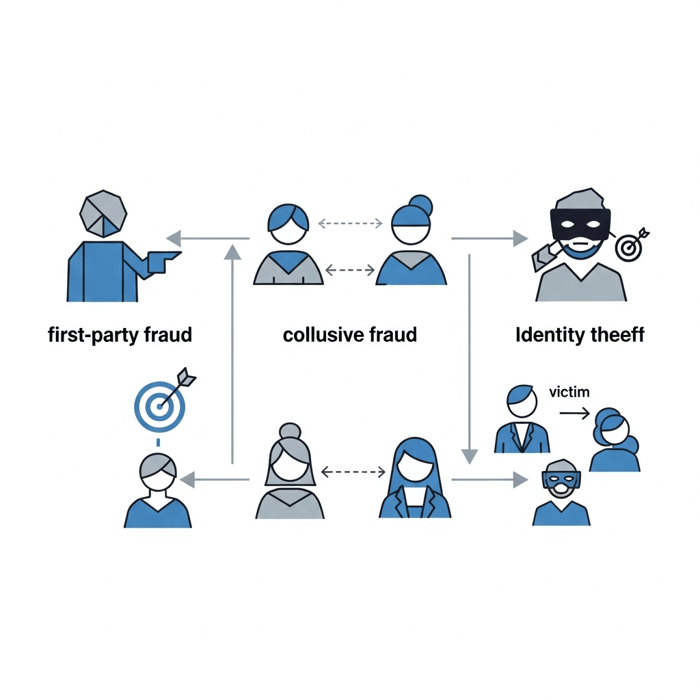
Fraud Type | Identity Used | Victim | Detection Difficulty |
|---|---|---|---|
First-party | Own identity | Lender, employer, insurer | High |
Second-party | Own identity, shared willingly | Lender, counterparty | Very high |
Third-party | Stolen identity | Identity theft victim | Moderate |
The core challenge with first-party fraud is that the tools built to stop third-party fraud simply weren't designed for it. You can't catch intent with an identity check. You need behavioral signals, pattern analysis, and historical context to spot someone whose documents are clean but whose actions suggest they never planned to follow through.
Common Types of First-Party Fraud
First-party fraud covers a wide range of schemes, but a few patterns show up consistently across industries.
Application Fraud
The fraudster applies for credit, benefits, or employment using accurate personal information but provides false context: inflating income, fabricating employment history, or misrepresenting their intent. The application passes because the identity is real. The deception is in the details around it.
Bust-Out Fraud
A borrower builds a solid credit history over months, earns higher limits, then maxes out every account and vanishes. No stolen identity needed. Just patience and a plan.
Chargeback Fraud
A customer makes a legitimate purchase, receives the goods, then disputes the transaction claiming it never arrived or was unauthorized. Also called friendly fraud.
Loan Stacking
Multiple loan applications submitted simultaneously across different lenders, before any single lender can see the others on a credit report. By the time the picture becomes clear, the funds are gone.
Refund and Return Fraud
Claiming refunds for products never returned, or returning damaged or counterfeit items in place of originals. Common in retail and e-commerce.
Insurance Fraud
Exaggerating or fabricating claims after a real insured event, or in some cases staging the event entirely while using a legitimate policy.
First-Party Fraud in Banking and Financial Services
Banking is where first-party fraud does its most expensive work. Credit misrepresentation, intentional loan default, chargeback abuse. These aren't edge cases. They're patterns baked into lending portfolios that most institutions are quietly absorbing as credit losses.
That misclassification is the real problem. When a borrower never intended to repay, that's fraud. But because the identity was legitimate and the application passed every check, the loss gets booked under credit risk. The fraud never gets investigated. The fraudster never gets flagged.
According to Experian's application fraud trends report, first-party fraud accounted for 29% in 2025, with Hidden Adverse History accounting for 48.2% of reported incidents. That's borrowers with concealed negative financial histories successfully misrepresenting themselves to lenders using real identities, clean-looking applications, and deliberate deception.
The dominant patterns in banking break down this way:
- Credit misrepresentation: Overstated income, hidden liabilities, and falsified employment used to qualify for products the applicant never honestly qualified for
- Bust-out schemes: Methodical credit building followed by deliberate default once limits are maximized
- Loan stacking: Simultaneous applications across lenders to draw down funds before any single institution sees the full picture
- Chargeback abuse: Disputing valid transactions after receiving goods, exploiting consumer protections meant for genuine theft victims
What makes banking uniquely exposed is the speed of credit decisions. Automated underwriting moves fast, and first-party fraud is designed to look clean under fast review. By the time repayment behavior reveals intent, the funds are gone. The fix isn't slower approvals. It's detecting behavioral signals and adverse history patterns at the application stage, before any money moves.
How First-Party Fraud Impacts Organizations
Direct losses are only part of it. Every fraudulent account written off as a credit loss instead of flagged as fraud represents a missed investigation, a fraudster left unchecked, and a pattern that repeats.
Recovery costs compound quickly. Fraud investigations, dispute processing, and compliance reviews carry real labor costs that rarely appear in fraud loss tallies. Reputational exposure adds another layer, especially for lenders and insurers where trust is the product.
The Systemic Cost
The deepest cost is organizational. When institutions cannot separate first-party fraud from genuine default, three things break down:
- Risk pricing becomes inaccurate because charge-off data is contaminated with intentional defaults that look like credit failures.
- Underwriting tightens bluntly across all borrowers instead of surgically against known fraud signals.
- Case history never accumulates, so repeat offenders cycle through undetected until the losses are too large to ignore.
First-Party Fraud Detection Methods
No single signal catches first-party fraud. The identity is clean, the documents check out, and the application passes standard review. Detection requires layering signals until intent becomes visible through behavior.
The methods that actually work:
- Behavioral analytics: How someone fills out an application matters. Hesitation patterns, autofill anomalies, and session timing can distinguish genuine applicants from scripted submissions.
- First-payment default monitoring: Borrowers who default on the first or second payment are disproportionately flagged as first-party fraud. The intent was never repayment.
- Network analysis: Shared device IDs, IP locations, phone numbers, or email patterns across multiple applications suggest organized fraud rings, even when each individual identity appears legitimate.
- Device intelligence: Emulators, VPNs, and device spoofing tools show up in first-party fraud cases far more often than in clean applications.
- Velocity checks: Multiple applications across lenders, insurers, or employers in a compressed window signal loan stacking or bust-out behavior before any single institution sees the full picture.
The pattern that keeps appearing in high-performing detection systems is combination. Any one of these signals alone produces too many false positives. Together, they produce intent.
Challenges in Detecting First-Party Fraud
The hardest part isn't finding the fraud. It's proving it.
With third-party fraud, there's a victim. Someone reports their identity stolen, disputes the account, and creates a paper trail. With first-party fraud, the person who committed it has no incentive to say anything. There's no complainant. No report. The account just goes delinquent and gets written off.
That absence of a victim is what lets first-party fraud hide so effectively inside normal credit loss data.
Why Intent Is So Hard to Prove
Intent is legally and analytically difficult to prove. A borrower who defaults might genuinely have hit hard times, or they might have never planned to repay. The outcome looks identical. Investigators need behavioral evidence collected before the default, not after, and most institutions aren't capturing it at the right moment.
The attribution gap makes everything downstream harder:
- Fraud teams can't build case history on losses that never get classified as fraud in the first place.
- Risk models can't separate intentional default from genuine financial distress without pre-default behavioral signals.
- Repeat offenders who cycle through multiple lenders leave no cross-institutional footprint unless someone is actively looking for it.
Human review compounds the problem. Experienced underwriters are trained to assess creditworthiness and employment history, not to spot behavioral signals that suggest deception. A clean application from a real person with real documents reads as a good application.
Human intuition wasn't designed to catch this.
First-Party Fraud in Hiring and Recruiting
Hiring gets less press than banking, but it's where first-party fraud has quietly become a serious business threat. The mechanics are identical: a real person, using their actual identity, submitting fabricated context around it. Inflated job titles, invented credentials, misrepresented employment dates. The identity check passes because the person is genuine. The fraud is in everything wrapped around it.
According to Experian, 45% of all false document submissions now occur in the employment sector. Nearly half. That's a signal that hiring pipelines have become one of the primary vectors for first-party fraud at scale.
What makes hiring uniquely exposed is what happens after the fraud succeeds. A borrower who defaults causes financial damage. An employee who misrepresented their credentials causes damage from inside the organization, accessing sensitive systems and creating insider threat exposure that can take months to surface.
Traditional screening wasn't built for this. Resume review catches typos. Reference checks catch exaggerations. Neither catches a real person who applied from a sanctioned country, submitted a resume seeded with fabricated employment, and is now one offer letter away from your codebase.
Detecting Fraud in Recruiting With Tofu
Recruiting fraud is a first-party fraud problem with an insider threat outcome. The person applying is real. Their deception lives in fabricated employment history, misrepresented credentials, and concealed locations. That's exactly the kind of intent gap that standard screening misses entirely.
FraudDetect screens every applicant across 40+ signals before a recruiter opens a single resume. Document metadata reveals fabricated employment histories that look clean on the surface. OSINT-based identity confirmation validates whether the LinkedIn or GitHub account actually belongs to the person claiming it. Network intelligence across 170+ customers means a fraudster flagged once is recognized everywhere. Fraud rings leave cross-applicant patterns that no single company could detect alone.
DeepDetect closes the gap that application screening leaves open. Even when a fraudulent applicant clears initial review, proxy swapping and deepfake manipulation during interviews are caught in real time: lip sync, eye movement, voice patterns, facial construction. The person who applied is verified against the person on screen, and again at every subsequent stage.
The detection principles are the same ones that work in banking: behavioral signals, network effects, and layered verification. Built for the one funnel where catching fraud late costs more than money. It puts a bad actor inside your organization.
Final Thoughts
Third-party fraud leaves a trail because the victim reports it. First-party fraud vs third-party fraud comes down to one difference: in first-party cases, there's no victim filing a complaint because the fraudster is the account holder. Your detection systems need to spot intent before default, not after, which means capturing behavioral signals at application time and building cross-lender intelligence that surfaces repeat patterns. The institutions that solve this aren't waiting for chargebacks to reveal the fraud. They're catching it at origination.