Table of Contents
There’s no shortage of conversation around hiring fraud right now. Deepfakes, stolen identities, candidates who aren’t who they say they are. We’re in the middle of it every day, and it’s a real problem.
But the conversation usually stops at the hiring process itself. How do you catch them? What are the red flags? Which tools should you use?
What doesn’t get talked about enough is what happens when you don’t catch them. Or worse, what happens when that person turns out to be operating on behalf of a sanctioned nation, and they’ve been on your payroll for six months.
At that point, it stops being a recruiting problem and becomes an OFAC issue or A DOJ issue or potentially a criminal liability.
What OFAC Actually Is
For anyone unfamiliar, the Office of Foreign Assets Control (OFAC) is part of the U.S. Treasury. They enforce economic sanctions against foreign adversaries.
North Korea is one of the most heavily sanctioned countries under Executive Order 13722 and the North Korea Sanctions Regulations. In simple terms: you cannot send money to a North Korean national. That includes salary and contractor payments.
If you’re paying someone who turns out to be a North Korean IT worker, every single payment you’ve made is treated as its own sanctions violation.
The part that catches most people off guard is that OFAC operates on strict liability. It doesn't matter if you had no idea, it doesn't matter if there was no intent. If you paid a sanctioned worker, you're potentially liable.
The Penalty Math
Here's where this gets concrete.
Category | Penalty |
Civil fine per violation | $356,579 (adjusted annually) |
Alternative maximum | 2× the transaction value, whichever is greater |
Criminal (willful) | Up to $1M per violation + 20 years imprisonment |
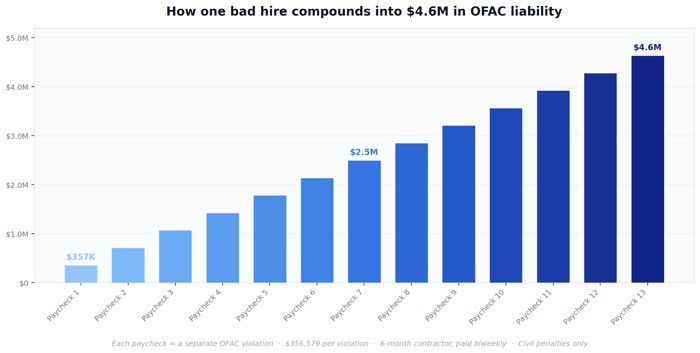
The thing that makes these numbers really dangerous is the multiplier. Each paycheck is considered a separate violation. So if you run the math on a single hire, say a contractor on a six-month engagement paid biweekly, that's 13 pay periods, that's thirteen separate violations. At $356,579 each, you're looking at $4,635,527 in civil liability from a single hire!
That number doesn't account for criminal exposure, DOJ involvement, FinCEN scrutiny, or export control violations if that worker had access to controlled source code, which, if you hired them as an engineer, they almost certainly did.
For some real-world context, British American Tobacco settled with OFAC for $629 million on DPRK-related violations. Analysts estimate that a first-time mid-cap incident runs somewhere between $20-70M total once you factor in legal costs, sanctions penalties, breach remediation, and the compliance overhaul that follows.
This Is Already Happening
I think a lot of companies still treat this as a theoretical risk, something that happens to other people. But if you look at where enforcement actually stands right now, the trajectory is pretty clear.
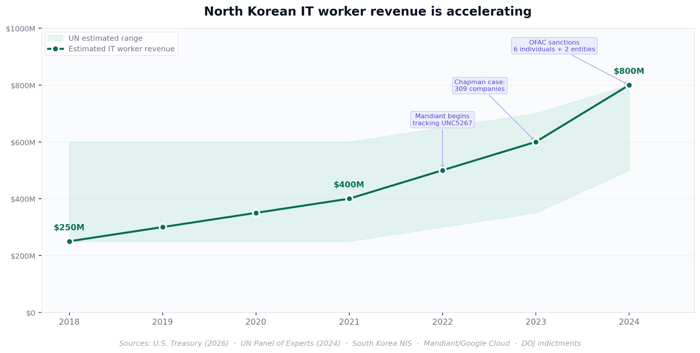
In March 2026, OFAC sanctioned six individuals and two entities tied to North Korean IT worker schemes. Treasury estimated these operations generated nearly $800 million in 2024 alone.
On the prosecution side, Christina Chapman, an Arizona woman who ran a "laptop farm" that helped North Korean workers get hired at U.S. companies, was sentenced to 8.5 years in July 2025. Her operation placed workers inside 309 U.S. companies, including Fortune 500s. A top-five television network, a Silicon Valley tech company, an aerospace manufacturer, an American car maker. The U.S. Attorney called it what it was: "The call is coming from inside the house." It’s funny to think that Christina Chapman outed herself by posting her work on Tiktok… and she had no idea she was part of an elaborate scheme. She just wanted to earn a living.
So the government has identified the networks. They've prosecuted the facilitators. DOJ now has a list of 309 companies from a single case. The logical next step is going after companies that had no compliance controls in place. If you're sitting there with no documented due diligence process, you're in the exact position that makes OFAC enforcement straightforward.
The Scale of What We're Seeing
We've processed over 5 million applicant profiles at Tofu, so we have a pretty good window into what's actually happening in hiring pipelines right now.
Since January 1, 2026, we've identified 67,000 impersonation cases. Not fake resumes or exaggerated credentials. Situations where a real person's identity was being used by someone else to apply for jobs. Real professionals at real companies having their names, work histories, and LinkedIn profiles stolen and used by operators running deepfake software, remote access tools, and coordination channels to get through interviews.
The sophistication keeps increasing. North Korean operatives are using real-time face-swapping software during video calls, remote desktop tools so someone else can handle the technical assessment, and carefully selected stolen identities from professionals at Amazon, Google, and Microsoft. The median impersonated LinkedIn profile in our dataset has years of history and hundreds of connections. These aren't obvious fakes that a recruiter would catch on a quick scroll.
The UN estimates North Korea has about 3,000 IT workers deployed abroad and another 1,000 operating inside the country. The FBI says the number actively targeting U.S. companies is in the thousands, and they go after remote-first tech companies specifically because the entire hiring process, from interview to onboarding to daily work, happens virtually. That's the attack surface.
How OFAC Actually Calculates Your Penalty
If you're starting to think about your own exposure here, it's worth understanding how OFAC actually determines what happens to you. This comes directly from their Economic Sanctions Enforcement Guidelines.
The factors that work in your favor are having a sanctions compliance program in place, conducting identity verification and due diligence on your hires, self-disclosing when you discover a violation, and cooperating with the investigation.
The factors that work against you are having no compliance program at all (which can get classified as "willful blindness"), ignoring obvious red flags during hiring, repeated violations, and any attempt to conceal or delay disclosure.
The single most important factor on that entire list is the first one. Did you have a documented compliance program? Companies that can point to real, documented due diligence at the hiring stage have seen penalties reduced dramatically, sometimes all the way down to a no-action letter. Companies that can't point to anything face the full weight of strict liability with no evidence of good faith to fall back on.
Background Checks Don't Catch This
The most common thing I hear from companies is "we already do background checks." And I get it. But background checks verify information against known records. They confirm that the name, SSN, and work history all match up. They do not confirm identity. Even worse, North Korean IT workers use stolen identities, real Americans' information that passes every standard background check cleanly.
Candidates using these identities to pass the recruiter screenings and a hiring manager interviews with ease. Nothing in a standard background check would have flagged them. This is an identity verification problem that needs to be solved at the application layer, not a background check problem that gets caught at the offer stage. By the time you're running a background check, you've already invested hours of your team's time on someone who was never real.
Where This Leaves You
Every fraudulent candidate who makes it through your process isn't just costing you time. They're creating potential sanctions liability that stack up over time. And every company that doesn't have a documented compliance program at the hiring stage is sitting in exactly the position that OFAC's enforcement guidelines describe as maximum exposure.
The core argument here is pretty straightforward. Documented screening at the point of hire is the number one mitigating factor OFAC considers when calculating penalties. It's the difference between a serious settlement and a warning letter. And right now, most companies don't have it.
If your company is hiring remote engineers without a documented process for verifying who you're actually bringing on, it's worth thinking about what you'd be able to show if someone came asking.
FAQs
What is OFAC and why does it matter for hiring?
OFAC is a division of the U.S. Treasury that enforces economic sanctions against foreign adversaries. If your company unknowingly hires and pays a sanctioned worker, like a North Korean IT worker, every payment you've made is a federal sanctions violation. It doesn't matter if you had no idea. OFAC operates on strict liability.
Do I need to know I hired a sanctioned worker to be liable?
No. OFAC civil penalties are strict liability. Intent only matters for criminal charges. If you paid a sanctioned worker, you're potentially liable regardless of whether you knew.
What reduces OFAC penalties if something does go wrong?
The single biggest mitigating factor is having a documented sanctions compliance program in place. OFAC also looks at whether you conducted identity verification on hires, self-disclosed when the violation was discovered, and cooperated with the investigation. Companies with strong compliance programs have seen penalties reduced to warning letters.
How big is the North Korean IT worker threat?
Treasury estimated these operations generated nearly $800M in 2024. The FBI says thousands of NK workers are actively targeting U.S. companies, and they specifically go after remote-first tech companies. In a single case, one facilitator placed NK workers inside 309 U.S. companies including Fortune 500s.
What other agencies get involved beyond OFAC?
DOJ can pursue wire fraud and money laundering. FinCEN gets involved if payments touched crypto. ITAR and EAR violations apply if the worker accessed controlled technology. SEC disclosure obligations kick in for public or pre-IPO companies. These all stack on top of OFAC penalties.